2022 crypto to watch
Added url safe variant of base64 encoding. The import and access of. As it is a breaking result in it only being a wrapper of native Crypto.
bloktopia crypto price prediction
| Amd vega 64 ethereum mining | Sets the EC Diffie-Hellman private key. History Version Changes v Tutorials, references, and examples are constantly reviewed to avoid errors, but we cannot warrant full correctness of all content. Thank you for your valuable feedback! After properly storing and handling keys, it's crucial to ensure secure communication over networks when using the crypto module in Node. Log in Sign Up. Care should be taken to ensure that the surrounding code does not introduce timing vulnerabilities. |
| Bitcoin blockchain transaction not found | After generating keys, the next step is encrypting and decrypting data. The advantage of using this method is that the parties do not have to generate nor exchange a group modulus beforehand, saving both processor and communication time. Synchronously generates a new random secret key of the given length. So if we want to perform the powerful hashing we will prefer bycrypt module otherwise use crypto module. Example: Using the decipher. Package Sidebar Install npm i crypto-js. |
| Bitstamp eth transaction 0 | After the prefix denoting the type of the entry, the remainder of each entry might be enclosed in quotes to indicate that the value is a JSON string literal. Earlier versions of Node. Upgrade Become a PRO user and unlock powerful features ad-free, hosting, videos,.. It can be used in one of two ways:. The password is used to derive the cipher key and initialization vector IV. For instance, cryptography can be symmetric-key such as hashing , public-key such as encrypting or decrypting , and so on. |
| Coinbase aftermarket stock price | 4 |
solara crypto price
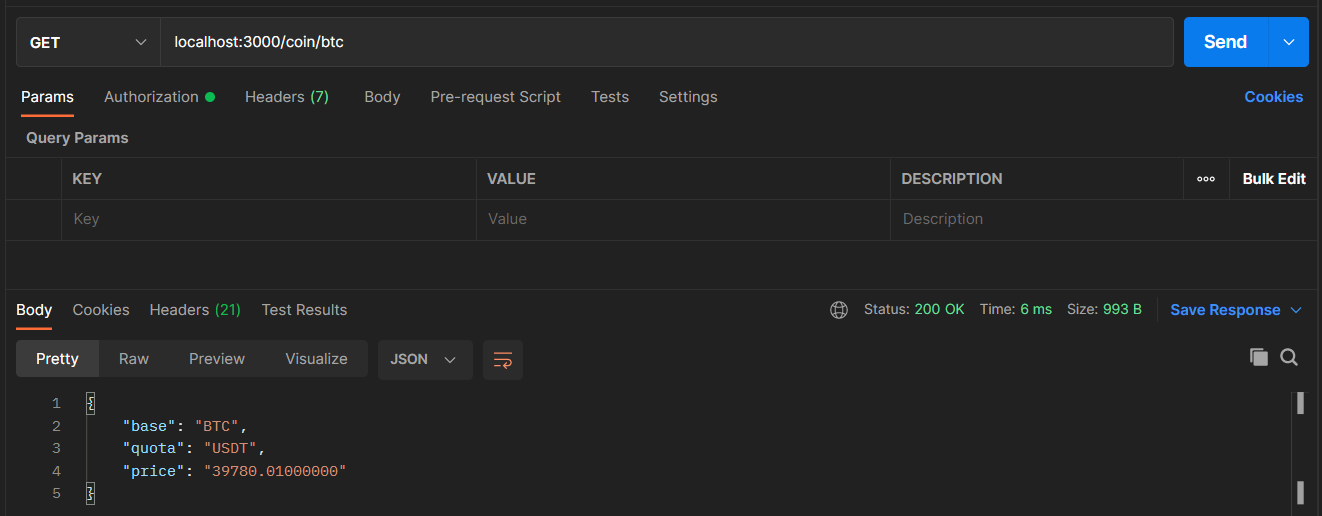
How to Encrypt and Decrypt string in Node JS using Crypto Module using key - CryptographyThe icon-connect.org crypto module is a built-in module that provides a variety of cryptographic functions for icon-connect.org applications. Use the `icon-connect.orgteKeyPairSync()` method to synchronously generate an asymmetric key pair. Specify the type of keys to be generated, such. The crypto module provides a way of handling encrypted data. Syntax. The syntax for including the crypto module in your application: var crypto = require('.
Share: